Anton Gostev recently wrote about a bug that will impact a lot of Veeam environments so I thought it would be best if I mentioned it here to help get the word out. Veeam have also created a KB article you can find here detailing this issue.
If your Veeam Backup & Replication console is showing a “Failed to check certificate expiration date” message upon opening the backup console, it means that your default self-signed certificate is about to expire.
A self-signed certificate is an identity certificate that is signed by the same entity whose identity it certifies. Veeam uses certificates to implement secure communications between your backup infrastructure components, as well as with any managed backup agents in your environment.
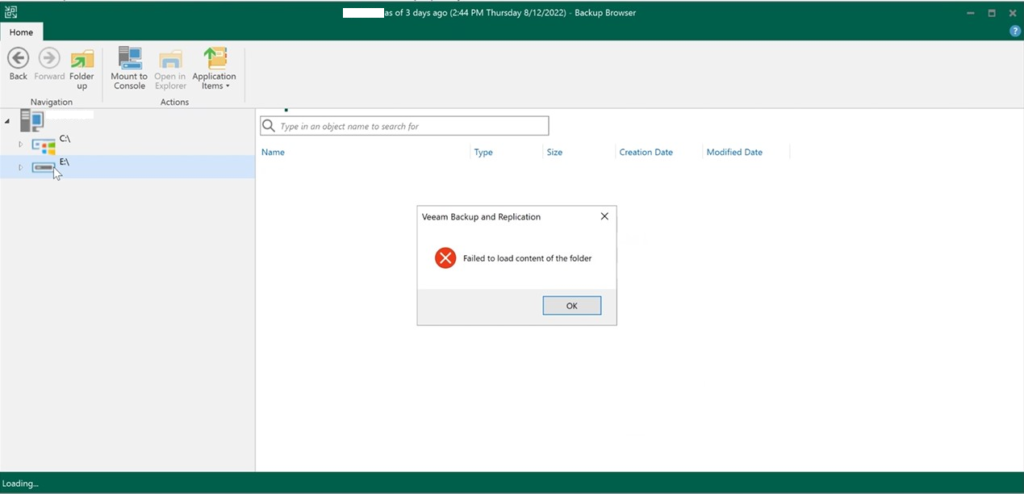
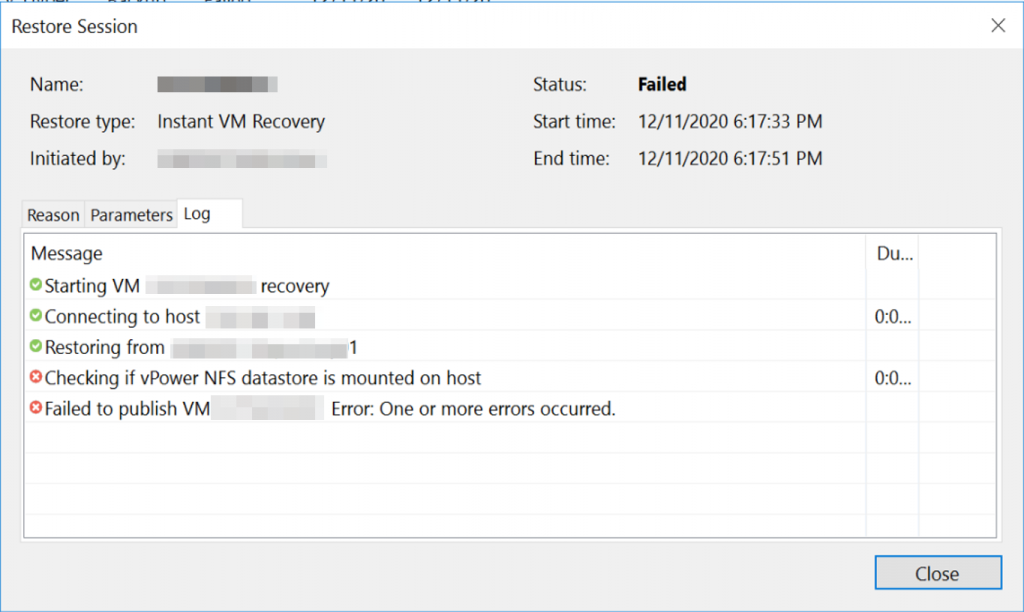
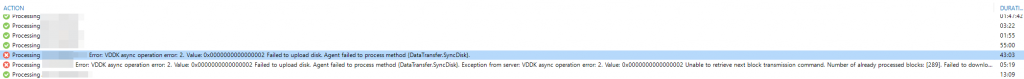
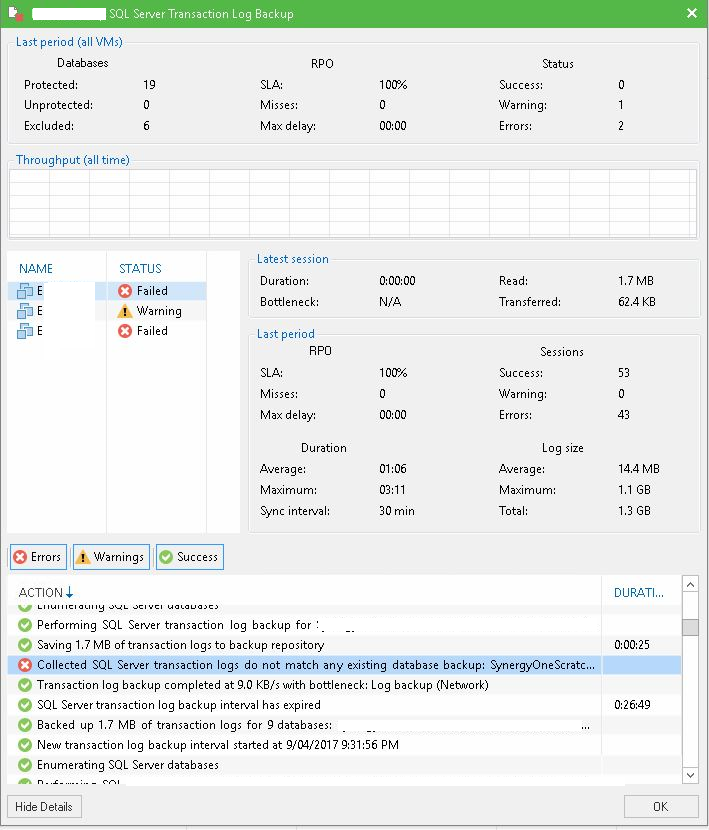
Now Self-signed certificates are automatically renewed every 12 months by your Veeam Server but due to a bug introduced in v9.5 U3a, the Veeam Backup Service will still have old information about the absolute certificate even after a new self-signed certificate is automatically generated. If you ignore this message, once the self-signed certificates are automatically renewed after 12 months, agent management functionality, as well as all granular restores will start failing.
Typically this will occur 1 year from the certificates creation date so the best course of action is to remedy the situation as soon as you see the error message and before the self-signed certificates expire. The fix is to manually generate a new certificate as described in this Veeam User Guide. Please note that this process will automatically restart the Veeam Backup Service so it’s is recommended to ensure no active jobs are running.
Worth mentioning, Veeam administrators can select or import their own certificate but most organisations are still using self-signed SSL Certificates which are generated when Veeam Backup & Replication is installed.